Get to know me
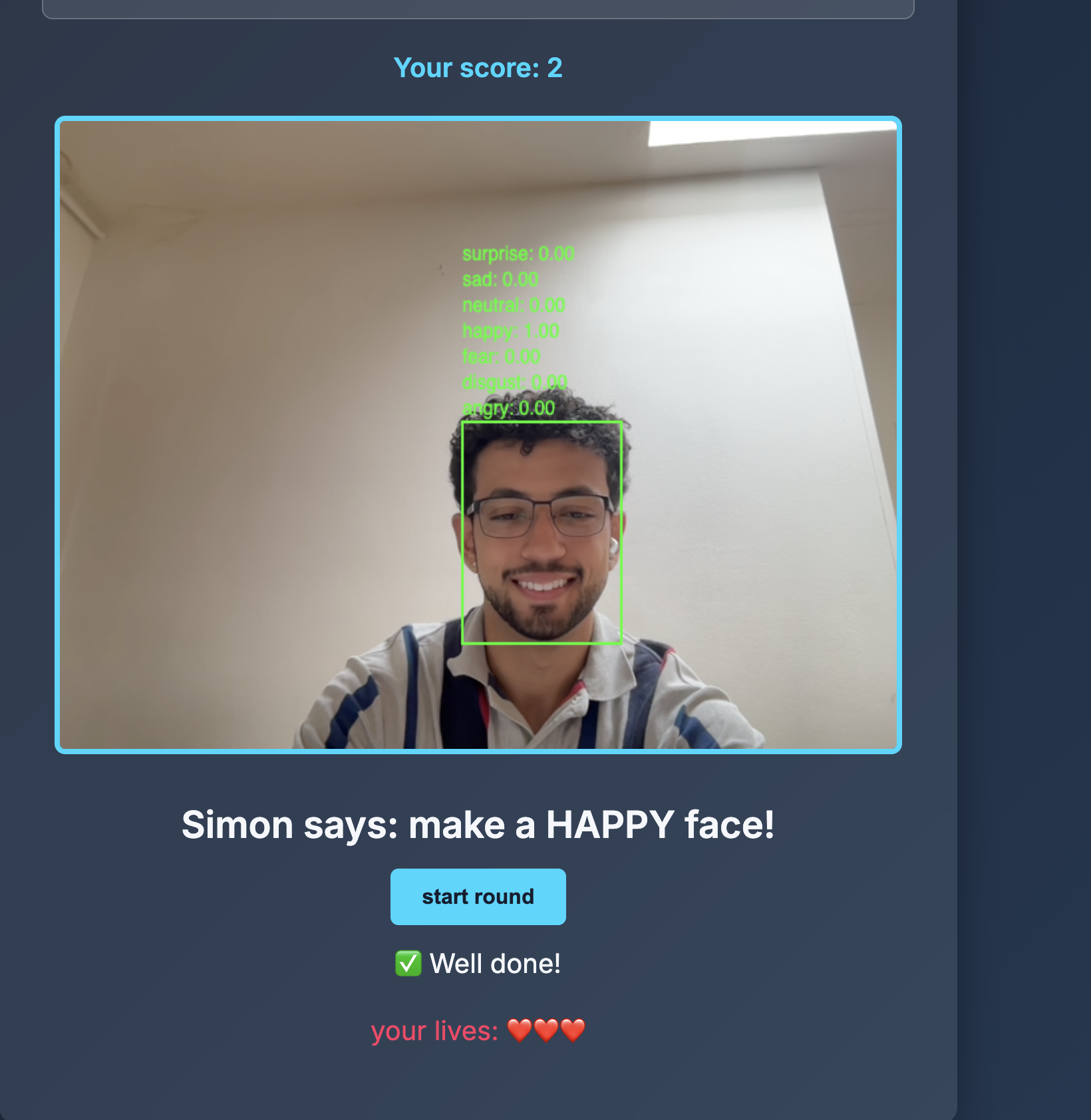
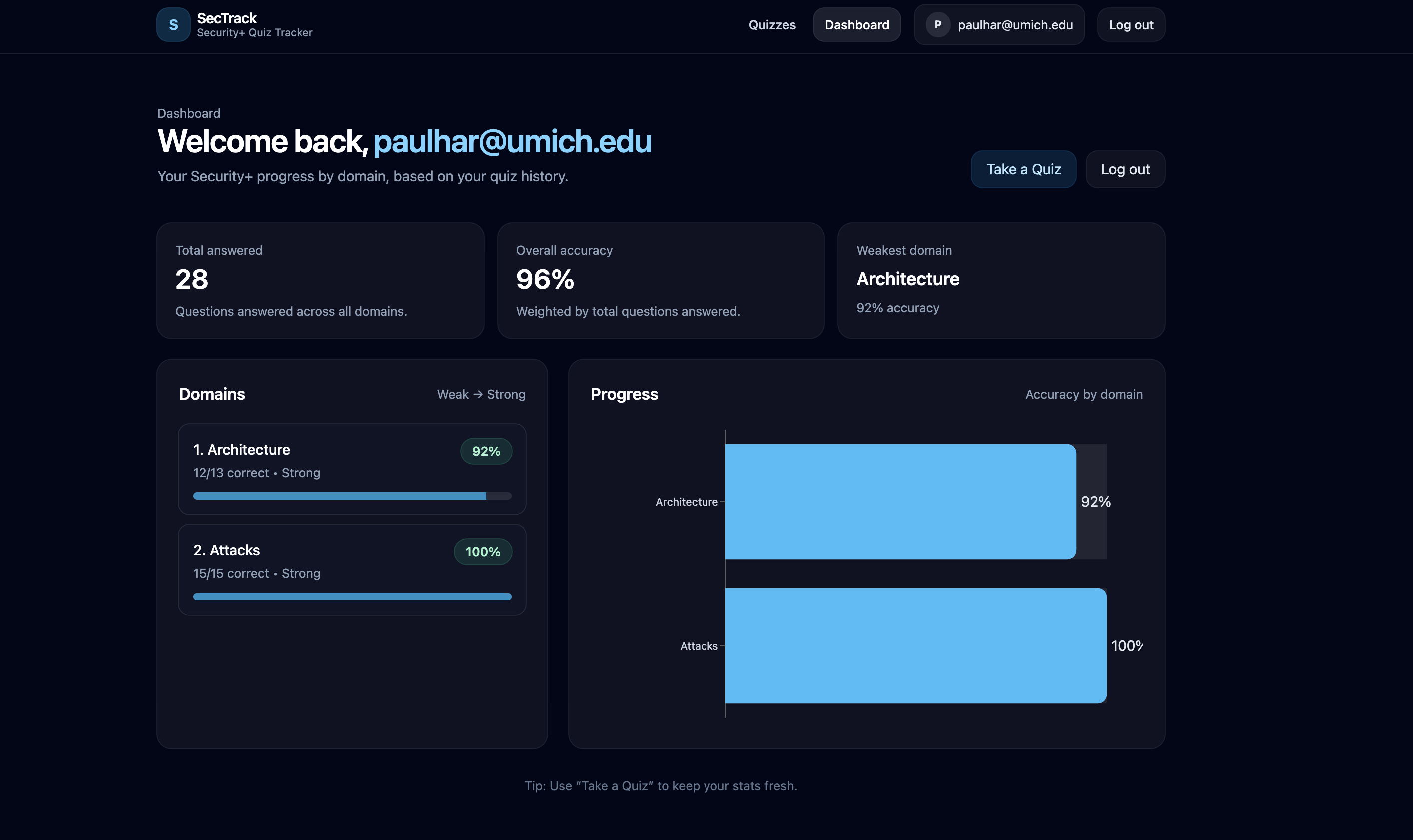
I'm Paul Harrison, a Software Engineering-focused Computer Science student at the University of Michigan. I enjoy building production-minded systems where clean architecture, strong UX, and measurable impact all matter.
From backend APIs and data workflows to frontend product experiences, I like owning features end-to-end. I care about pragmatic engineering: writing maintainable code, validating with real users, and continuously improving performance and reliability.
Feel free to contact me here.